use of a smart card for authentication For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential . Mar 23, 2022. #5. BigBlur said: Apple Pay is basically just an umbrella term for Apple's payment method. It doesn't always mean contactless payment via NFC. There may be an NFC chip, but that still doesn't mean you can do NFC/contactless stuff. This article says there is a NFC controller in the Touch Bar.QUICK ANSWER. NFC tags and readers communicate wirelessly with each other over very short distances. Tags store a small amount of data .
0 · smart card multi factor authentication
1 · smart card identity
2 · smart card based identification system
3 · smart card authentication step by
4 · smart card authentication protocol
5 · enable smart card log on
6 · enable smart card authentication
7 · authenticate using your smart card
The nRF52832 and nRF52840 devices have a built-in NFC radio which can be .
smart card multi factor authentication
medical tags rfid
Smart cards let you use extra checks too, like a code or your body, to make authentication even safer. Smart cards use complex codes to keep data safe and stop .How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Smart cards let you use extra checks too, like a code or your body, to make authentication even safer. Smart cards use complex codes to keep data safe and stop . For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential .
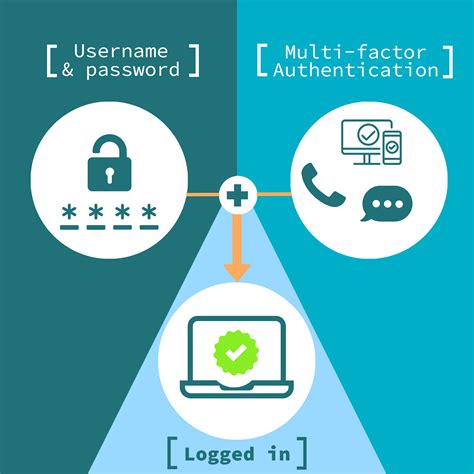
Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and .
Smart cards are tamper-resistant portable storage devices that can enhance the security of tasks such as authenticating clients, signing code, securing e-mail, and signing in . Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, .Smart card authentication requires two things: the smart card itself and a pin entered by the user. With smart cards there are two different ways to authenticate yourself into a system, there is .Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, .
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data .
A smart card is a secure microcontroller that is typically used for generating, storing and operating on cryptographic keys. Smart card authentication provides users with smart card devices for .How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Smart cards let you use extra checks too, like a code or your body, to make authentication even safer. Smart cards use complex codes to keep data safe and stop .
smart card identity
For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential .Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and . Smart cards are tamper-resistant portable storage devices that can enhance the security of tasks such as authenticating clients, signing code, securing e-mail, and signing in . Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, .
Smart card authentication requires two things: the smart card itself and a pin entered by the user. With smart cards there are two different ways to authenticate yourself into a system, there is .
Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, . Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data .

Mag strip is still used as a fallback method. . Some terminals will allow you to use the .
use of a smart card for authentication|authenticate using your smart card