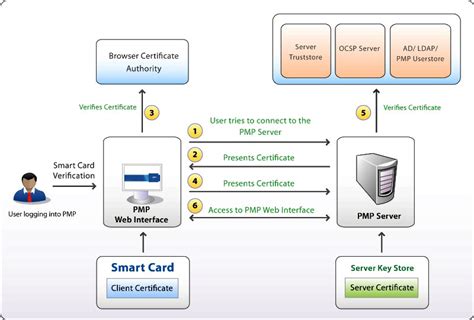
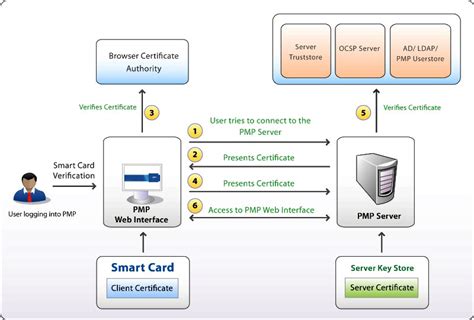
implementing smart card authentication Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a . Upon launching the app, you’ll be greeted with a straightforward interface. Locate the “Read NFC Tag” option and tap on it. Bring your NFC card close to iPhone’s NFC reader, which is usually located at the top of the device. Hold the card steady for a few moments, allowing iPhone to recognize and read the card’s information.
0 · smart card certificate authentication
1 · smart card authentication step by
2 · enable smart card windows 10
3 · enable smart card log on
4 · authenticate using your smart card
5 · active directory smart card configuration
6 · active directory smart card authentication
7 · active directory smart card
Cards with chip-and-PIN and near-field (NFC) technology typically aren’t vulnerable to magnetism the same way magnetic stripes are. . The bottom line: If your credit card isn’t working, contact your card issuer for a .
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a .This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. It includes the following resources about the architecture, certificate management, and services that are related to smart card use:
hp digital sender smart card login
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers. Implementing Smart Card Authentication: Plan and Prepare: Evaluate Security Needs: Decide what safety needs and rules your group must follow. Find What’s Needed: Know the machines, apps, and things that will require smart card verification. For new Windows installations, we recommend Windows Hello for Business or FIDO2 security keys. This article describes the virtual smart card technology and how it can fit into your authentication design. Virtual smart card technology uses cryptographic keys that are stored on computers that have the Trusted Platform Module (TPM) installed.
These Windows Domain configuration guides will help you configure your Windows network domain for smart card logon using PIV credentials. There are many useful pages and technical articles available online that include details on configurations and using generic smart cards.
hp 850 g1 smart card reader not functioning
Discover the benefits, challenges, and best practices for implementation. Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and . This document covers the basic steps required to set up an Active Directory domain environment for smart card authentication, including considerations before provisioning YubiKeys for smart card login.Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, pocket-sized cards with embedded integrated circuits or "chips" that can process data. Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.
how to view smart health card
The process for setting up smart card authentication by configuring AD can be simple. This article by Microsoft covers an in-depth overview of configuring smart card authentication with third-party CAs. Here’s a quick overview of the configuration process: Download the certificate chain from the CA that issues certificates to smart cards.
This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. It includes the following resources about the architecture, certificate management, and services that are related to smart card use: Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers. Implementing Smart Card Authentication: Plan and Prepare: Evaluate Security Needs: Decide what safety needs and rules your group must follow. Find What’s Needed: Know the machines, apps, and things that will require smart card verification. For new Windows installations, we recommend Windows Hello for Business or FIDO2 security keys. This article describes the virtual smart card technology and how it can fit into your authentication design. Virtual smart card technology uses cryptographic keys that are stored on computers that have the Trusted Platform Module (TPM) installed.
These Windows Domain configuration guides will help you configure your Windows network domain for smart card logon using PIV credentials. There are many useful pages and technical articles available online that include details on configurations and using generic smart cards.
Discover the benefits, challenges, and best practices for implementation. Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and .
This document covers the basic steps required to set up an Active Directory domain environment for smart card authentication, including considerations before provisioning YubiKeys for smart card login.Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, pocket-sized cards with embedded integrated circuits or "chips" that can process data.
smart card certificate authentication
smart card authentication step by
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.
enable smart card windows 10
how to use yubikey as a smart card with bitlocker
how to use secure credit card smartly
$64.00
implementing smart card authentication|authenticate using your smart card