which remote authentication protocol supports smart cards Remote Desktop Services enables users to sign in with a smart card by entering a PIN on the RDC client computer and sending it to the RD Session Host server in a manner similar to authentication that is based on user name and password. Smash Bros Ganondorf Nintendo Amiibo NFC Card Legend of Zelda Breath of the Wild. Brand .
0 · remote authentication quiz flashcard
1 · remote authentication flashcards
2 · remote authentication dial in
3 · remote access test flashcards
4 · remote access card quiz
5 · remote access card flash cards
The most complete, accurate and reliable reference source for January 9, 2005 - .
In a Remote Desktop scenario, a user is using a remote server for running services, and the smart card is local to the computer that the user is using. In a smart . See more You can configure the redirection behavior of smart card devices from a local . Remote Desktop Services enables users to sign in with a smart card by entering a PIN on the RDC client computer and sending it to the RD Session Host server in a manner similar to authentication that is based on user name and password. You can configure the redirection behavior of smart card devices from a local device to a remote session over the Remote Desktop Protocol (RDP). For Azure Virtual Desktop, we recommend you enable smart card redirection on your session hosts using Microsoft Intune or Group Policy, then control redirection using the host pool RDP properties.
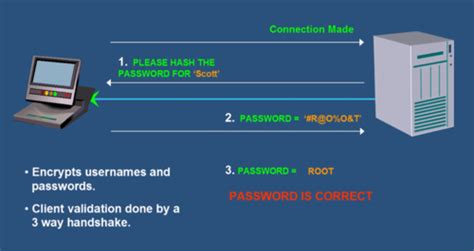
RADIUS. Both RADIUS and TACACS+ are protocols used for centralized authentication, authorization, and accounting with remote access. Remote access clients send authentication credentials to remote access servers. When you use a password to sign in interactively to a domain account, Windows uses the Kerberos version 5 (v5) protocol for authentication. If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates.We adapt a pair of dynamic IDs to realize the user's anonymity, and present a novel nonce-based authentication approach. Our protocol eliminates all identified security flaws in original protocols. Furthermore, high performance and other good functionalities are preserved.
EAP offers the strongest security by providing the most flexibility in authentication variations. EAP can support authentication mechanisms, such as token cards, smart cards, certificates, and public key encryption authentication. Introduction. Internet of things is a network connecting traditional objects (fridges, vehicles, doors, trees, applications.), which has the possibility to communicate without human intervention. Smart Card-based CredSSP works similarly to passwords. The NLA portion works just the same. The difference is the creds themselves. It turns out RDP emulates the smart card hardware and literally passes hardware commands back and forth over the channel. This is, incidentally, why it takes so long for RDP sessions to start when using smart cards .
remote authentication quiz flashcard
In 2009, Hsiang and Shih (2009) proposed a static ID based remote authentication protocol using smart cards. This scheme supports computation efficiency by utilizing only hash function operations.BeyondTrust allows you to use a virtual smart card on remote systems during a support session. Review the prerequisites to using BeyondTrust's smart card feature. Remote Desktop Services enables users to sign in with a smart card by entering a PIN on the RDC client computer and sending it to the RD Session Host server in a manner similar to authentication that is based on user name and password.
You can configure the redirection behavior of smart card devices from a local device to a remote session over the Remote Desktop Protocol (RDP). For Azure Virtual Desktop, we recommend you enable smart card redirection on your session hosts using Microsoft Intune or Group Policy, then control redirection using the host pool RDP properties.RADIUS. Both RADIUS and TACACS+ are protocols used for centralized authentication, authorization, and accounting with remote access. Remote access clients send authentication credentials to remote access servers.
keyfob rfid blocker bag use
When you use a password to sign in interactively to a domain account, Windows uses the Kerberos version 5 (v5) protocol for authentication. If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates.We adapt a pair of dynamic IDs to realize the user's anonymity, and present a novel nonce-based authentication approach. Our protocol eliminates all identified security flaws in original protocols. Furthermore, high performance and other good functionalities are preserved.EAP offers the strongest security by providing the most flexibility in authentication variations. EAP can support authentication mechanisms, such as token cards, smart cards, certificates, and public key encryption authentication. Introduction. Internet of things is a network connecting traditional objects (fridges, vehicles, doors, trees, applications.), which has the possibility to communicate without human intervention.
Smart Card-based CredSSP works similarly to passwords. The NLA portion works just the same. The difference is the creds themselves. It turns out RDP emulates the smart card hardware and literally passes hardware commands back and forth over the channel. This is, incidentally, why it takes so long for RDP sessions to start when using smart cards . In 2009, Hsiang and Shih (2009) proposed a static ID based remote authentication protocol using smart cards. This scheme supports computation efficiency by utilizing only hash function operations.
remote authentication flashcards
static shielding bag vs rfid blocking
sling bag with rfid blocking pocket
The NFL has announced the full schedule for the wild card and divisional round of the 2015 NFL Playoffs, following a packed Week 17 to conclude the regular season. One team .
which remote authentication protocol supports smart cards|remote access test flashcards